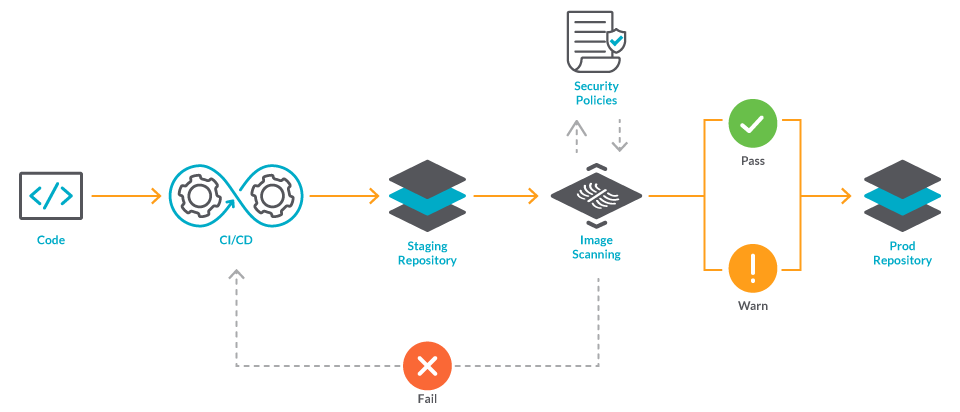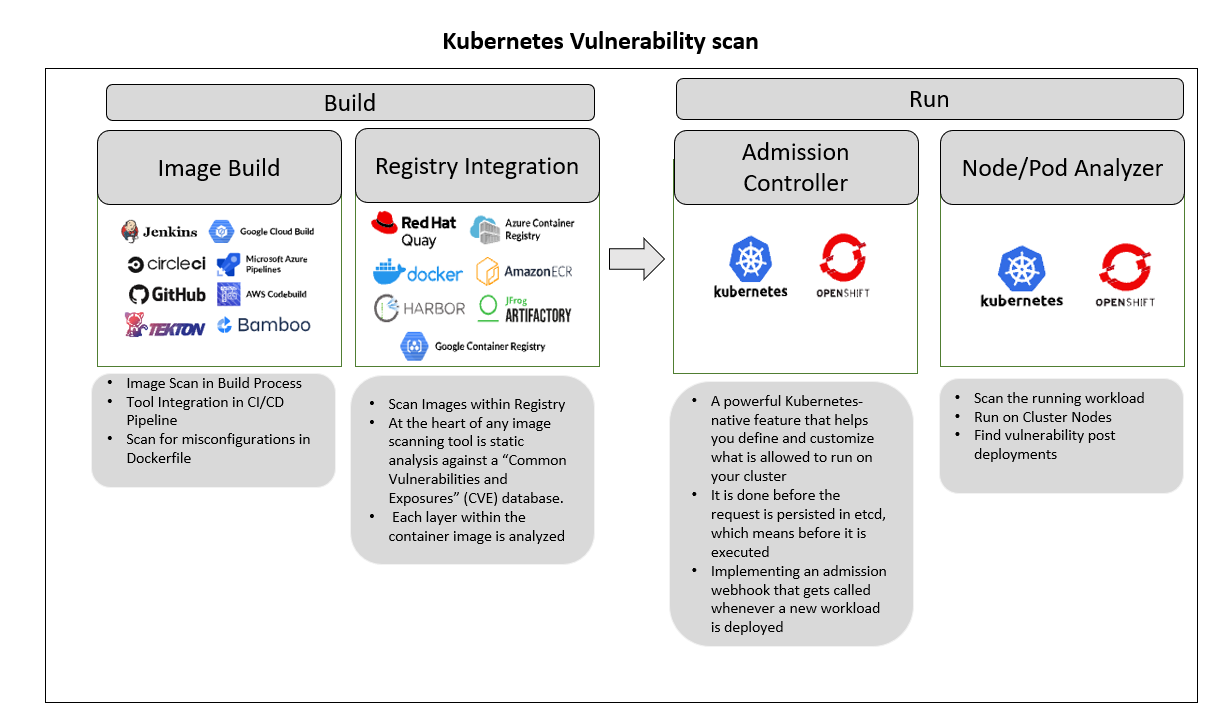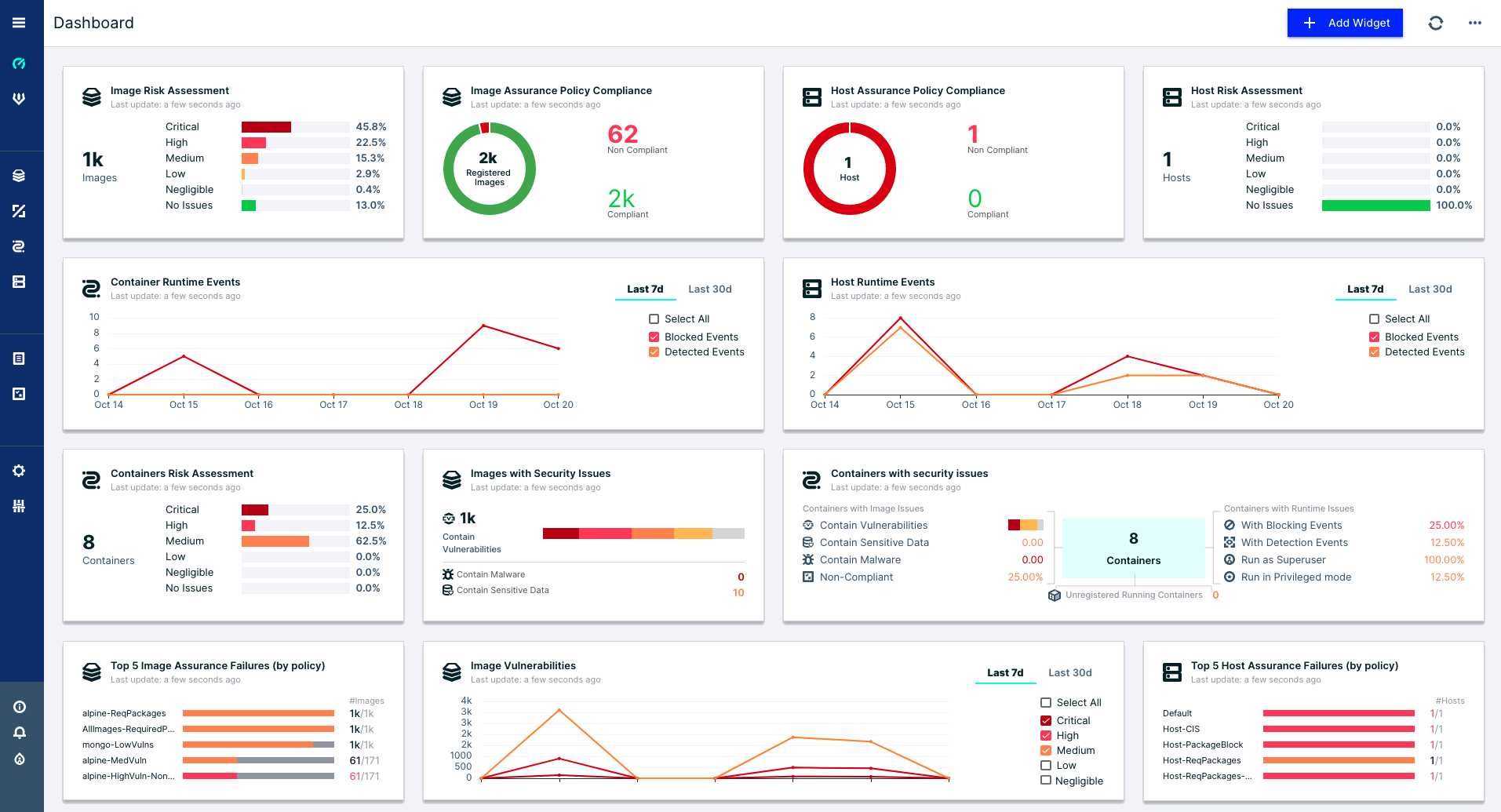
How to build a CI/CD pipeline for container vulnerability scanning with Trivy and AWS Security Hub | AWS Security Blog

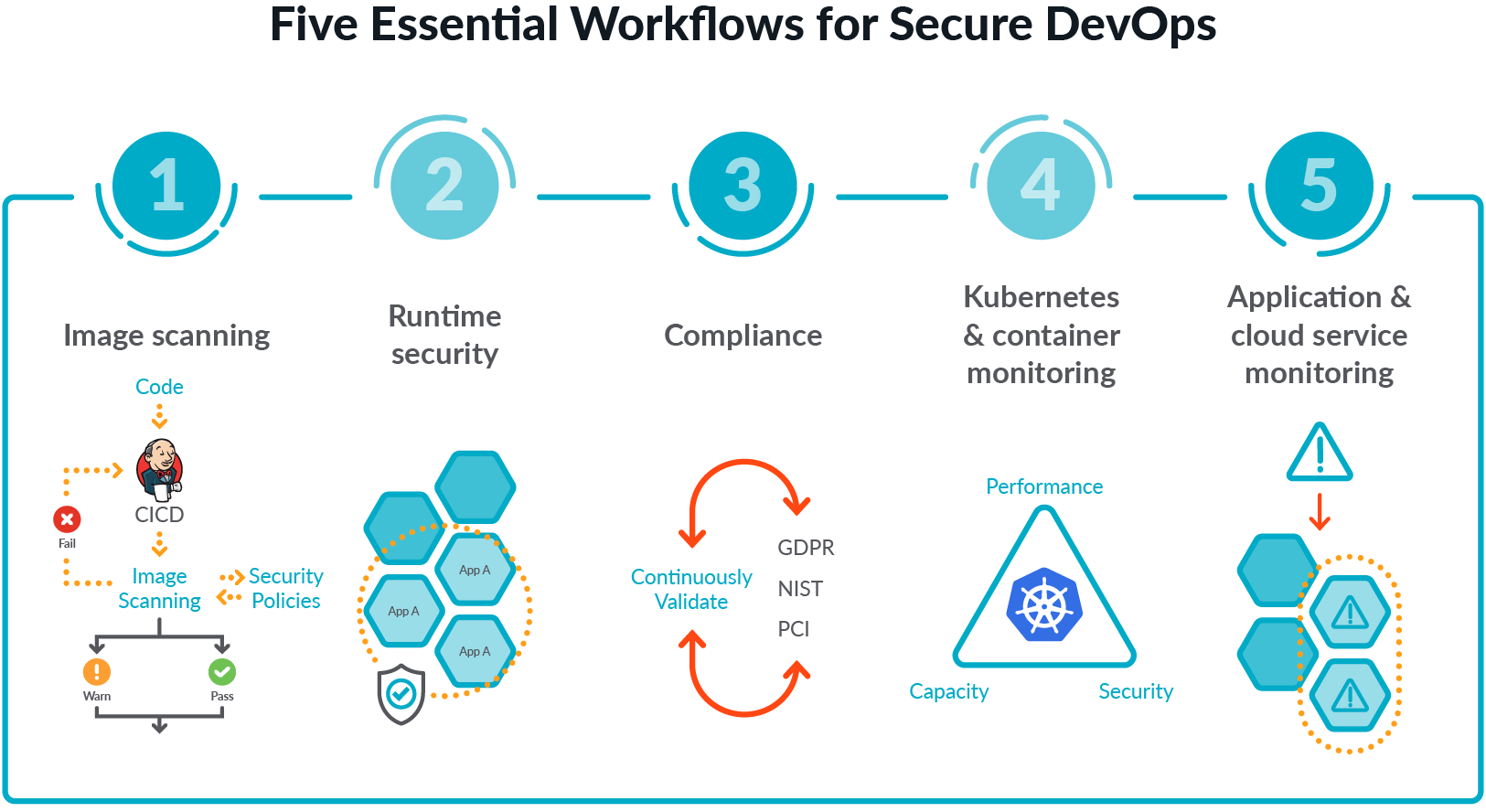
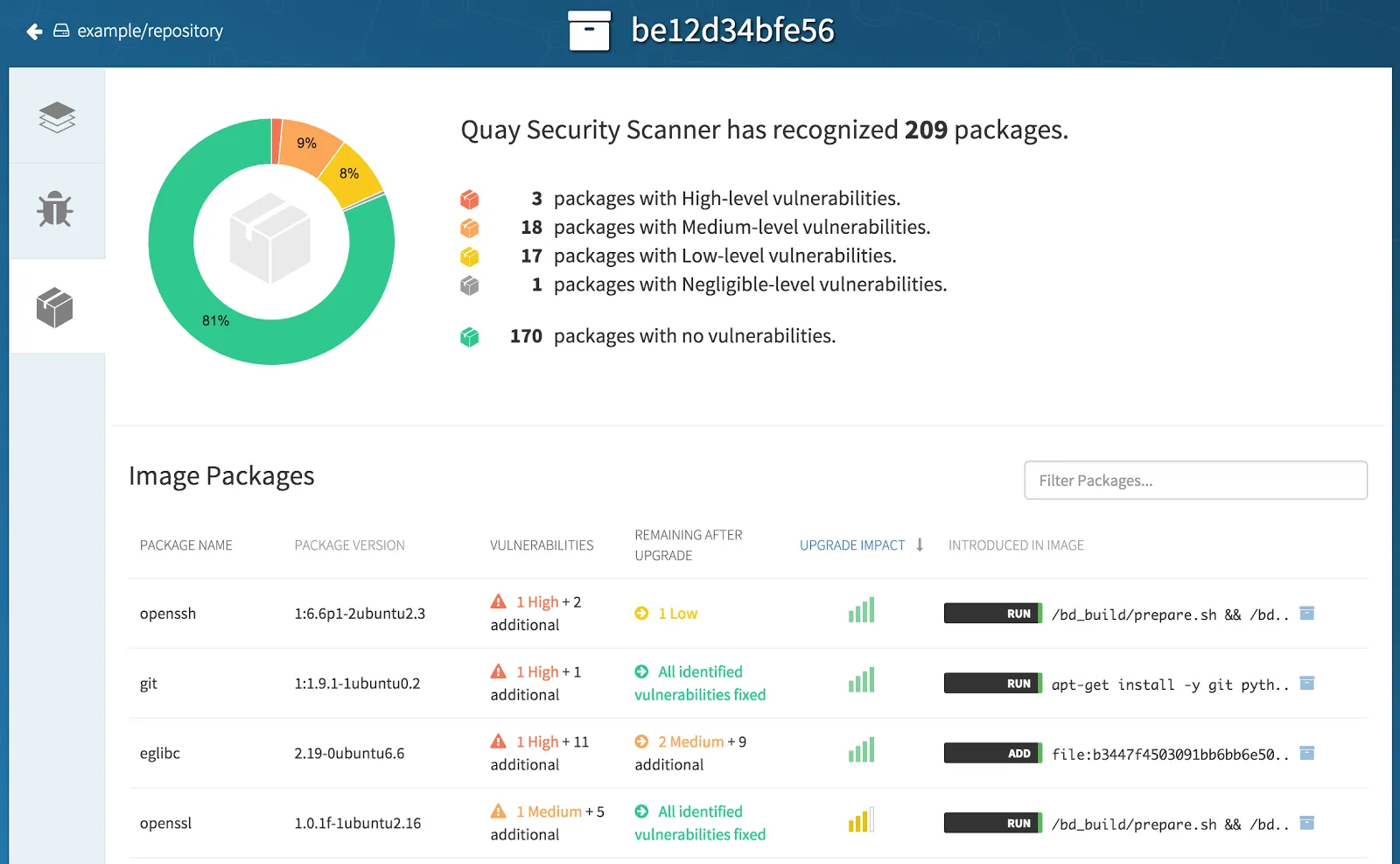
Guard against security vulnerabilities in your software supply chain with Container Registry vulnerability scanning | Google Cloud Blog

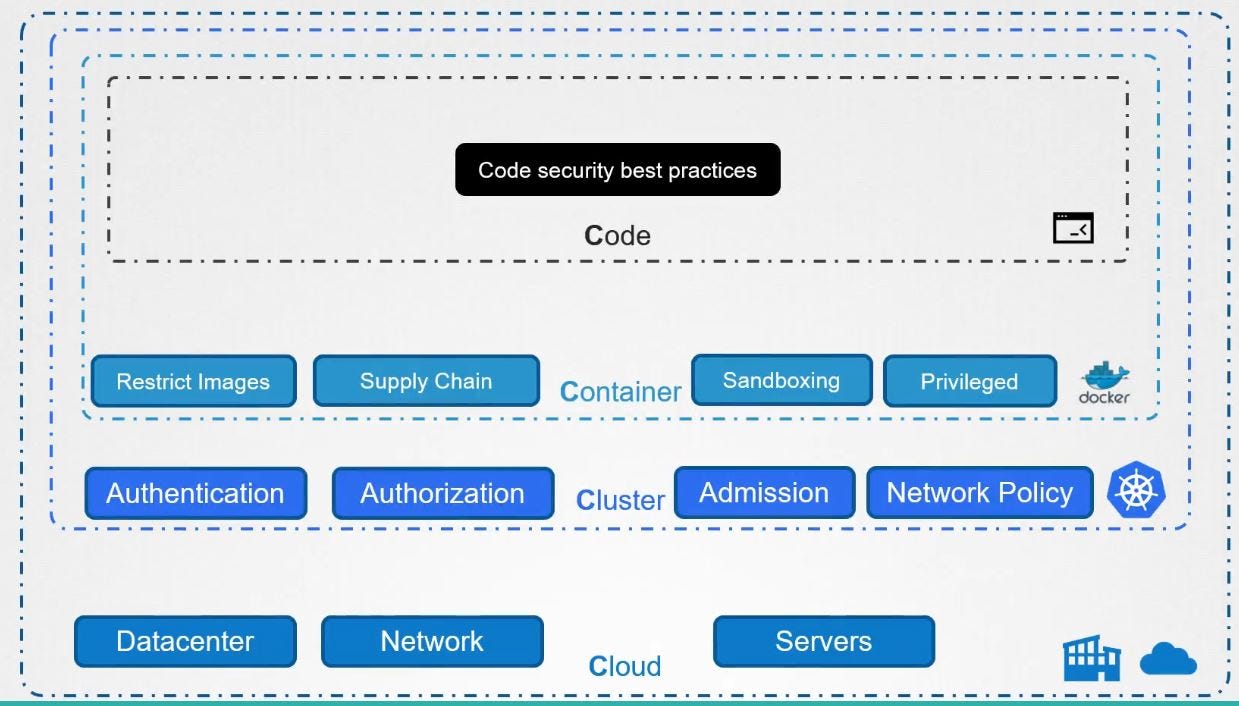
Operator best practices - Container image management in Azure Kubernetes Services (AKS) - Azure Kubernetes Service | Microsoft Docs